Data leakage is a widespread problem around the world. According to a survey conducted by IBM in December, many internet users have already suffered from the problem. The alarming numbers point to the importance of the International Data Privacy Day, which takes place last Tuesday. The objective of the event is to create awareness among users of the need to protect their personal information on the Internet.
Even though it is common, conduct such as saving online payment data, repeating the same password on multiple sites, using public Wi-Fi networks, and using social media profiles to log in can pose a risk to data security. In this article, Techidence presents seven tips to protect your online information.
1. Do not save payment data
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2018/l/E/kW2e0qSm2B8zdAH4qfOw/computer-banking.jpg)
Although very convenient, the practice of saving credit card data when shopping online is far from secure. Consumers who adopt this habit are actually putting their finances at risk. That’s because even the most trusted stores can fail to protect customer data and end up exposing thousands of sensitive information online. That’s what happened in 2013 with some websites after an error in the site’s session control. In addition to the risk of data leakage, there is also the possibility that stores may charge for improper purchases.
2. Make privacy adjustments in social networks and other services
Social networks are real showcases. Users reveal details about their life and routine, which can attract not only the attention of purely curious stalkers but also malicious people. To do this, you need to go beyond restricting profile privacy. This is because on Instagram, for example, there is a gap that allows all private posts to be accessed and shared with people outside the social network.
On any platform, the best tip to avoid unpleasant situations is always to redouble the attention to the posted content. Try not to post photos and videos that expose sensitive information. It is also worth “cleaning up” the list of friends and followers and make sure that the profile is followed only by trusted people. Other tips involve disabling automatic photo tagging, disabling the location, and blocking annoying users.
3. Do not repeat the same password on multiple sites
/s.glbimg.com/po/tt2/f/original/2014/10/02/021932374-password.jpeg)
Most people have the habit of repeating the same password on different sites. The reason is simple and even understandable: with a variety of online platforms, it would be very difficult to remember the combinations used in each of them.
However, it has a price: adopting the same code makes it easier for hackers to act and opens loopholes for credential stuffing, which occurs when criminals steal a site’s credentials and use them to violate other services of interest.
Therefore, in addition to using unique passwords, it is important to make long combinations, with more than nine or ten characters and mixing capital and lowercase letters, numbers, and special symbols. To further enhance code security, try replacing letters with numbers. If you’re having trouble creating the combination, try using online generators.
4. Do not use social networking profiles to log in to other sites
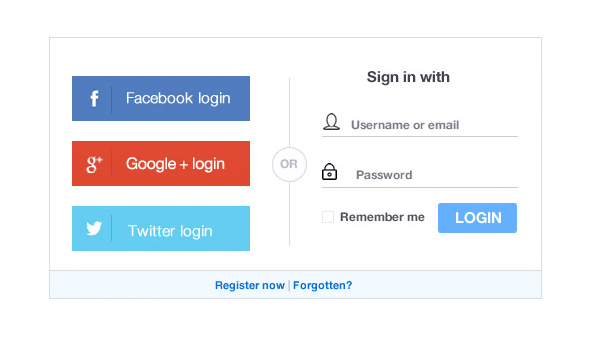
When registering on a website, it is common for users to be asked to log in from their account on another service, such as Google or Facebook. Although it saves time, “single sign-in” is not a completely secure alternative since it gives the site access to personal information contained in the email account or social network, paving the way for privacy violations. Whenever possible, choose to register in the traditional way.
5. Review Application Permissions
It is common for applications to request permission to access contacts or files on the phone storage, as well as to use the camera, microphone, and geographic location. In fact, some of them do not work without these concessions, but there are cases of apps that unduly access users’ privacy, usually for marketing purposes. Fortunately, with a few simple tips, you can prevent applications from accessing your data.
6. Enable two-step verification

As the name already says, the two-step verification makes it difficult for intruders to enter an extra phase in the login process. With the procedure, even if the offenders have obtained the credentials, they will not be able to access the account. To do this, they would also need to have the person’s cell phone in hand, since the final authentication code is usually sent to the device. You can enable two-step verification for services like Gmail, WhatsApp, and Instagram.
7. Avoid using public Wi-Fi networks
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2018/F/O/ks1RCYRHa5BvcZzTyjRA/rede-wifi-celular-home.jpg)
Attracted by the possibility of accessing online services outside the home and free of charge, many users connect to open Wi-Fi networks. However, this commonplace and seemingly harmless attitude hides a risk: criminals can create false public networks to steal data from users. From the login, hackers are able to track all visited sites and even steal passwords and other personal information provided.
To avoid criminal interceptions, always use a virtual private network (VPN) to connect to the Internet. By encrypting the connection, the VPN helps prevent third parties from accessing your device and capturing the data you send and receive. Never connect to Wi-Fi networks whose origin is unknown.
This post may contain affiliate links, which means that I may receive a commission if you make a purchase using these links. As an Amazon Associate, I earn from qualifying purchases.

