When storing cryptocurrencies the security behind them is the password we have and how well we store it so that others cannot access it. Many users prefer a special physical USB keychain to store that password so that it is not published in any cloud or online. But what happens when hackers manage to infiltrate even offline physical wallets?
It’s happening. Over the past few months, attacks on cryptocurrency users who store their data in physical cryptocurrency wallets have been on the rise. In principle, these wallets are the safest alternative there is for storing cryptocurrencies (unless you lose them). But they are not invulnerable.
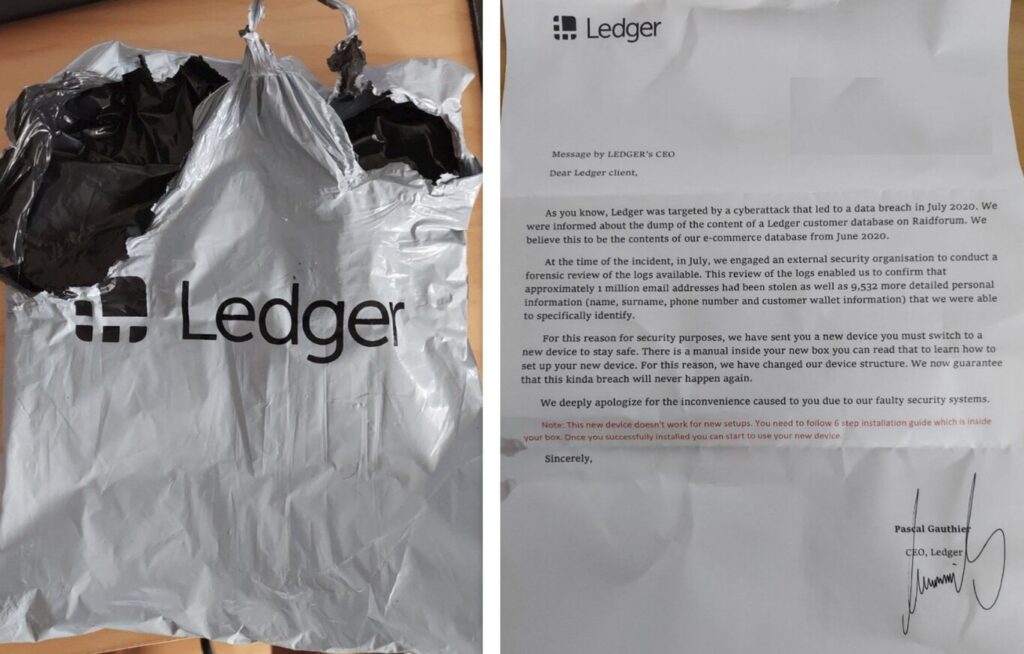
The Ledger physical wallet that is not a Ledger wallet
As recounted in Vice, Ledger users are receiving fake physical wallets. Ledger is a company dedicated to the manufacture of physical wallets for cryptocurrencies. The company has different products on the market, especially USB keychains to securely store cryptocurrencies.
Last year Ledger suffered a massive hack that compromised hundreds of thousands of accounts. Users had their data compromised and are still suffering the consequences ever since. One of those consequences appears to be this scam. Users are receiving new keychains that are real and from Ledger, although in reality, they are not.

Since their physical addresses and data were leaked, hackers are sending physical wallets in Ledger’s name. The key fobs arrive along with instructions and a letter purportedly signed by Ledger’s CEO. The letter asks users to replace their current physical wallet with this new one because the data was recently compromised.
As indicated by Ledger itself, what is behind this is a Ledger Nano X (the company’s real product) but tampered with. A flash drive is added to it containing an app that prompts the user to enter their 24-word recovery phrase. This phrase is sent to the scammers who can then access the users’ accounts and transfer all the cryptocurrencies.
According to Ledger, this phrase should never be shared, even with the company itself. They say that much of the responsibility ultimately lies with the user and his awareness that he is playing with important and valuable data in between.
This post may contain affiliate links, which means that I may receive a commission if you make a purchase using these links. As an Amazon Associate, I earn from qualifying purchases.

