Do you remember Thunderbolt? That security flaw detected some time ago that put the security of users through their computer ports in danger? Well, you should know that it’s back now. A report published by the Eindhoven University of Technology has just revealed that the Thunderbolt security system, present through the connection ports of peripherals and Intel equipment, could be the perfect gateway to the attacks of millions and millions of computers around the world.
Researcher Björn Ruytenberg’s investigation reveals that if a computer hacker gains access to a computer for as little as five minutes, he or she may be perfectly capable of taking over the login data and gaining full access to the personal data and information contained on the user’s computer.
But who can be affected by this problem and in what way? Thunderbolt ports are on many Windows, Linux, and macOS computers, which means that many people can be affected. According to this researcher, Rutenberg, all equipment developed and manufactured between 2011 and 2020 would be affected by this problem. The worst of it? That no software update can solve the problem. Hence, the only possible solution is to redesign the silicon system of computers.
Fortunately, no hacker – no matter how good he is – can remotely access our computer to exploit this bug. It would be necessary, in any case, for the criminal to be physically present, which complicates – and greatly complicates – the possibility of our computers being attacked.
How Do I Know if my Computer is Affected?
The truth is that, even if you know you are affected by this very common problem, there is not much you can do to solve it. Still, it doesn’t hurt to check it out. How? We’ll tell you.
The people responsible for the research project led by Ruytenberg have created open-source software called Thunderspy. It’s a completely secure tool, which you can use to check whether your computer is indeed a candidate for a hack. It is compatible with both Windows and Linux, so if this is the case, you can follow these instructions:
1. First, go to the Thunderspy page. This is a secure site, so don’t worry. Click on “Spycheck for Windows” to download the tool created by this research team to your computer.
2. Then, unzip the downloaded file so that you can access the installation files. Open Thunderspy and select your language. You can only choose between French and English. Accept the terms of use.
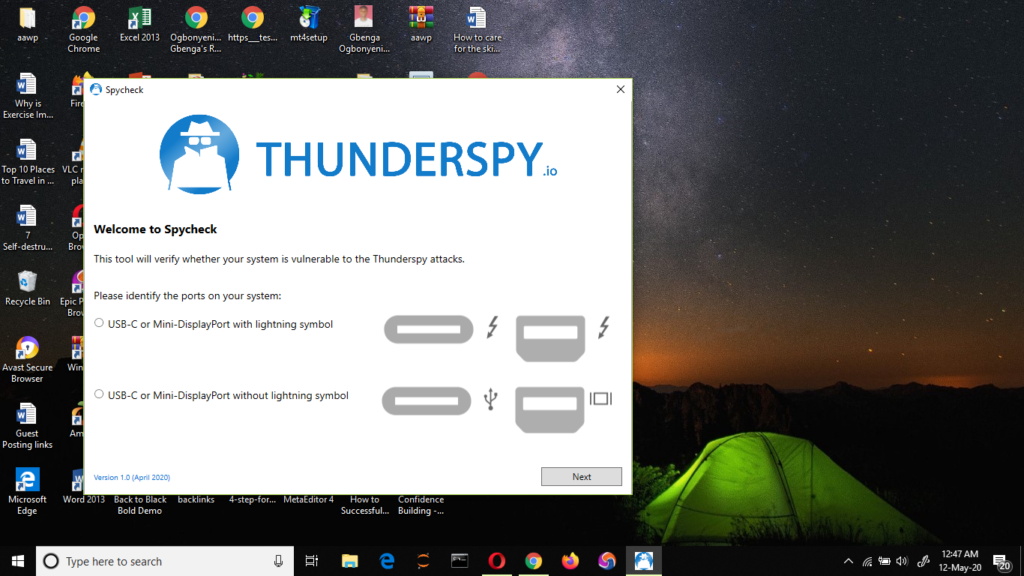
3. Now the system will ask you to identify the ports on your computer. Choose the correct option by checking whether or not the ports have the lightning icon (as you can see in the image). The program will then tell you whether or not your computer is vulnerable to this problem. Users with a vulnerable computer have the option to disable Thunderbolt in the BIOS/UEFI so that the ports will only work as USB.
In any case, and taking into account that an attacker must have physical access to the machine to perpetrate an attack, it is wise to keep the computer always under surveillance and try not to leave it unattended, whether we are working with it in a public or shared space.
This post may contain affiliate links, which means that I may receive a commission if you make a purchase using these links. As an Amazon Associate, I earn from qualifying purchases.

