When it comes to protection, passwords are the gateway to keep the smartphone safe and out of the reach of others. Passwords help in the event of theft and robbery and prevent unauthorized persons from accessing data such as phone books, social networks, and financial applications.
Today, mobile phone manufacturers have invested in different types of biometric security, such as facial recognition and iris recognition, in addition to traditional ways of entering passwords. With so many options available, many users may have questions about what is the best way to protect the device. Check below for some tips on the main types of biometrics.
Biometrics means applying metrics to biological characteristics, that is, using attributes of the human body, such as fingerprint and iris, to create security standards. This identification helps to keep confidential data protected. However, there are also other ways to protect the device, such as PIN and standard passwords, in addition to other recent technologies.
PIN Code

The PIN is a numerical code, usually four to six digits, that needs to be entered every time the phone is locked. This system is more secure than the standard, but makes the unlocking slower and requires the user to memorize the code. To make it easier, many people end up using birthday dates and repeated digits, which makes the method easier to bypass.
Therefore, it is important to create longer passwords and avoid linking them to something easy to guess. Changing the password regularly also helps to make the phone more secure.
To activate the feature on Android, just go to “Security” and “Screen Lock”. The current password will be requested to continue. Then tap on PIN and set a new four to six-digit password.
On iOS, go to “Settings” and then “Touch ID and Code”. The current PIN will be requested. Then click “Change Code”, enter the current PIN and then the new PIN.
Password

The difference between PIN and password is that the former only allows numeric characters, while the latter also allows letters and symbols. This process makes the password longer and more time consuming to type, but makes it difficult for third parties to access it.
It is important to choose a pattern that interpolates numbers, letters, and symbols to make it more secure.
To trigger the feature on Android, just follow the same steps above. Go to “Security” and “Screen Lock”, enter the current password, and touch “Password” to set the new code.
On iOS, go to “Settings” and then to “Touch ID and Code”. The current PIN will be requested. Then touch “Change Code” and enter the current PIN. When entering the new PIN, go to “Code Options”. A tab to add the alphanumeric code will open. Just select the option and enter the new password.
Lock Pattern (drawing)
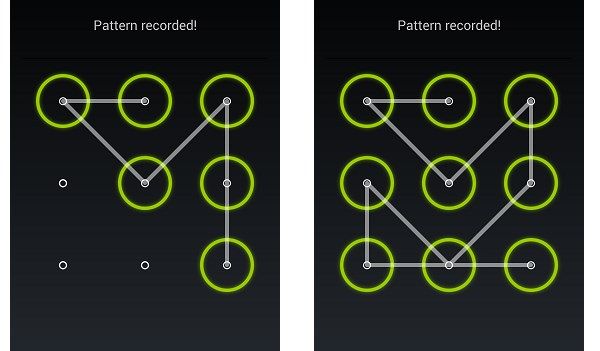
On Android phones, you can enable the option of screen blocking by sliding or drawing. Some devices offer a nine-point grid, allowing users to set a default drawing. Theoretically, this would give the possibility to create more than 400,000 patterns.
However, recent research indicates that people tend to opt for the minimum number of nodes, which is four, which decreases the possibility of possible combinations to 1,624 and makes the code easier to guess. Also, it is more common for these passwords to start at the top left and to use letters like N, O, C, S, and M. This makes this form one of the least secure to block the phone.
However, there are some tips for creating strong and easy to remember passwords:
- Try not to start the password from a corner and avoid using letters of the alphabet;
- Use more than four nodes to make the password stronger and more difficult to guess;
- Include crosses and use the same point more than once;
- Change the password frequently.
To activate the lock, just go to “Settings” and “Security and Screen Lock”. You will then be prompted for the current PIN or password.
In the next step, choose the drawing option and set the new default. Touch “Continue”, confirm the password and select “Finish”.
Another security option for this type of locking hides the pattern when entering it. To do this, just go to “Settings”, “Security” and disable the “Make the pattern visible” option.
Fingerprint

This type of biometrics works by recognizing the user’s fingerprint and is quite common in banks, academics, and other computer systems. The use of fingerprint is very safe and unlocks the device quickly, bringing agility and convenience, since it is not necessary to enter the PIN at all times.
However, the method also has some disadvantages and gaps. It is possible to pick the user’s fingerprint on a surface and place it on the sensor to unlock the device. Besides, you can create a set of artificial fingerprints to fool the system or even wait for the user to sleep and position his finger on the reader. Therefore, it is important to keep a close eye on this kind of system.
There are different types of fingerprint technology used in today’s smartphones. Apple, for example, started using the sensors from iPhone 5S, through the Home button. The system lasted until the iPhone 8 when it fell into disuse with the arrival of the iPhone X. The manufacturer uses capacitive sensors that trace bumps on the finger instead of making a 2D copy of the printout, like other systems.
With this, the company claims there’s a 50,000 chance that someone else’s fingerprint will unlock the phone. To enable the function, touch “Settings” and “Touch ID and Code”. Then enter the PIN code and touch “Add Fingerprint”.
Touch the sensor with your finger, without pressing. Keep your finger on the button until you feel a quick vibration. Repeat the movement until the process is finished and then adjust the edge scanning. Click continue to validate the new fingerprint.
On Android phones, the print sensor can come built into the front, sides, back (to make the screen bigger), and most recently, into the screen itself. Older models use the optical sensor, which scans the finger by throwing light on it.
The ultrasonic system, known to be present in the most modern cell phones on the market, such as the recently launched Galaxy S21, by Samsung, works by projecting ultrasonic waves that detect digital details more accurately. The system interacts with the skin of the finger and returns with 3D images more accurately compared to the previous system.
However, this model also has loopholes. Heat marks on the screen or glass films can irritate the sensor and cause failure.
To activate the system on Android, go to “Settings” and touch “Biometrics and Password”. On some devices, the option may be in “Lock and Security Screen”. When you open the option, all forms of phone biometrics will be listed. Go to “Fingerprint ID”. Password PIN will be requested.
Touch “New fingerprint” and press the finger on the sensor repeatedly. When finished, select “Finish”.
Important to remember that after five wrong attempts, the phone will lock the screen for a period, usually 30 seconds.
Facial Recognition

In recent years, cell phone manufacturers have placed great emphasis on facial recognition. This is because the system is faster and safer than a fingerprint and takes up less space on cell phone screens. Even so, the system has security holes.
If the user’s face is registered in dark or very bright places, the phone will have difficulty in recognizing the face. Also, 2D technology can be fooled by user photos and natural changes such as aging.
To activate the function on Android, go to “Settings” and touch “Biometrics and Password”. On some devices, the option may be in “Lock and Security Screen”. Then choose “Facial Recognition”. Enter the current PIN and click start. Position the face in the center of the screen and follow the instructions indicated to finish.
Face ID

Face ID is Apple’s facial recognition system. It works by 3D facial scanning, which makes the method more secure. According to the manufacturer, the chances of cheating the system are one in a million.
The system operates through a set of sensors, with more than 30 thousand points, which track the user’s face in 3D. Apple guarantees that the system is capable of adapting to users’ physical changes, such as hairstyle, beard growth, and accessories such as hats and scarves.
To configure the system on iOS, go to “Settings” then “Face ID and Code”. Enter the current PIN and touch “Configure Face ID”. Then adjust the face in the center of the device and click continue. Follow the steps indicated to complete the facial registration.
Iris Scanning
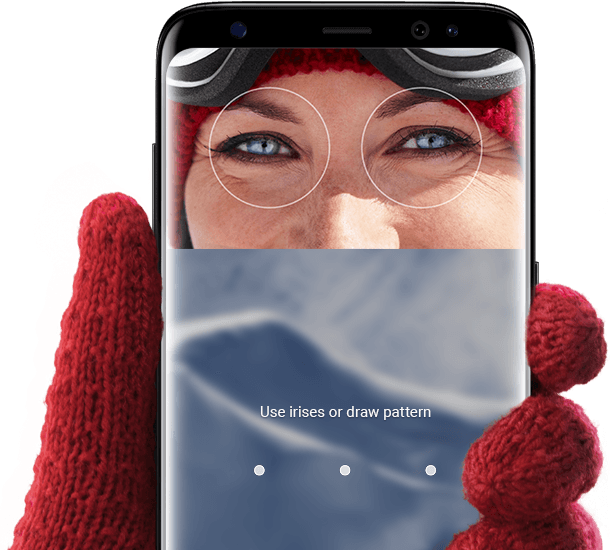
Iris scanning is considered a very secure form of biometric authentication since the iris is more unique than fingerprints. The disadvantage is that the method can take longer than the others since one has to look directly at the sensor and wait for recognition.
The sensor works by emitting visible or infrared light waves. These make a clear, detailed, and high contrast mapping of the user, including the center and edge of pupils and the patterns drawn in the iris. However, the method also leaves some security holes, as some experts can recreate the characteristics of the owner and confuse the system.
The pattern is used in some Samsung cell phones, such as the Galaxy S8. The company combines 3D facial recognition with the iris reader to make unlocking the phone even more secure.
To set the function on Android, go to “Lock and Security Screen” and select “Iris Reader”. The next thing is to adjust the vision in the indicated space, keep your eyes wide open and wait for the procedure to be completed.
Smart Lock
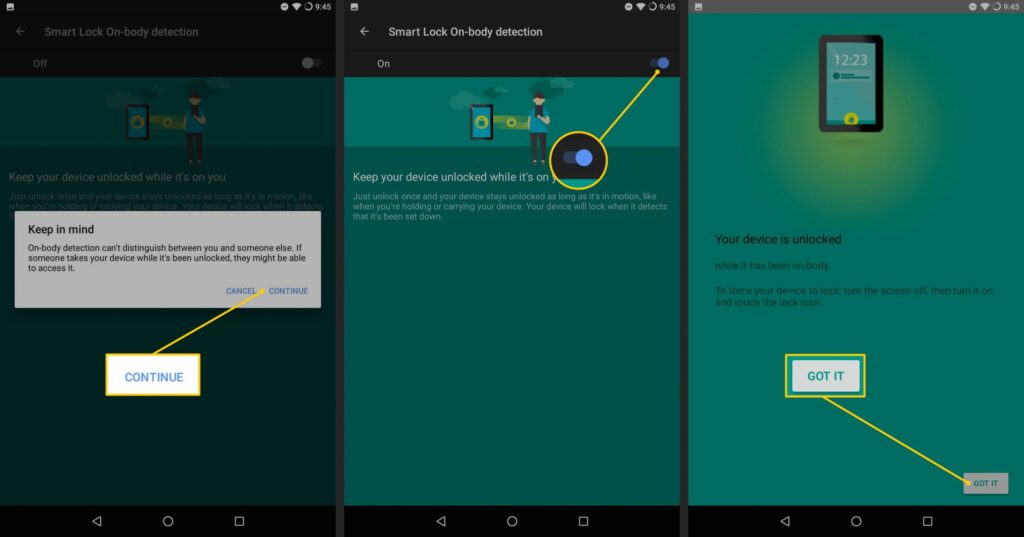
Another very useful feature on the devices is Smart Lock. The Android system allows the phone to remain unlocked automatically whenever the user is in a trusted location, near a trusted device, or the owner.
To configure the function, go to “Settings” → “Security” → “Smart Lock”. Then enter the current password and configure the system based on other trusted devices, trusted locations, or detection in your pocket.
This post may contain affiliate links, which means that I may receive a commission if you make a purchase using these links. As an Amazon Associate, I earn from qualifying purchases.

